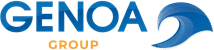
Live data shows how security measures are working
Determine how risk mitigation measures are performing for the desired time period and make appropriate follow-up decisions based on current data.
Time period
Choose the period of observation according to your needs.
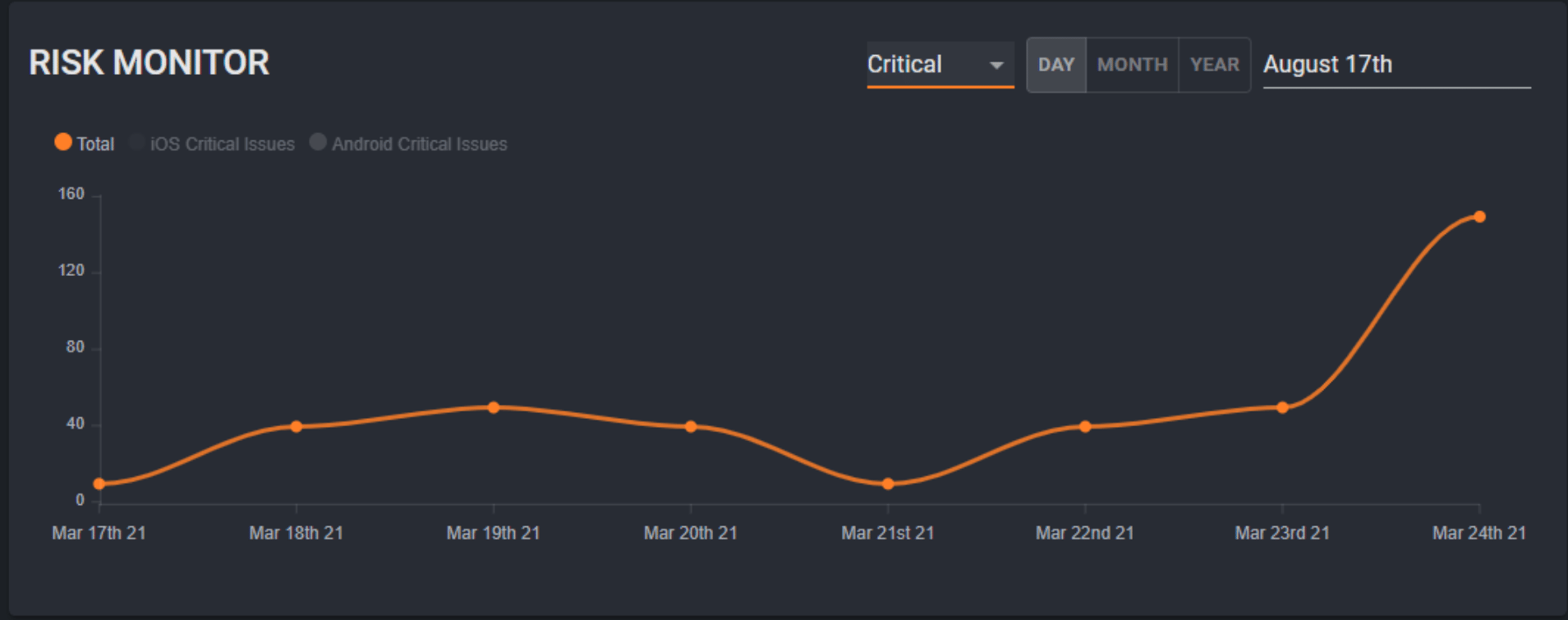
CLEAR 360° VIEW
Gain valuable insights through
- Development of risks in terms of risk classification
- Change in overall risk (+/-)
- Distribution and quantity of devices with critical risks
Identify whether the entire company or only parts of it are affected and derive precise measures from this.

DASHBOARD
Keep an eye on all critical security vulnerabilites and see on 1-click on which device they are located.
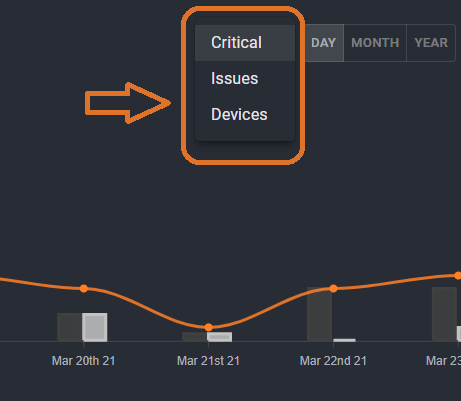
KPI
Use the Risk Indicator to determine the current security status of your company or your sub-organizations.
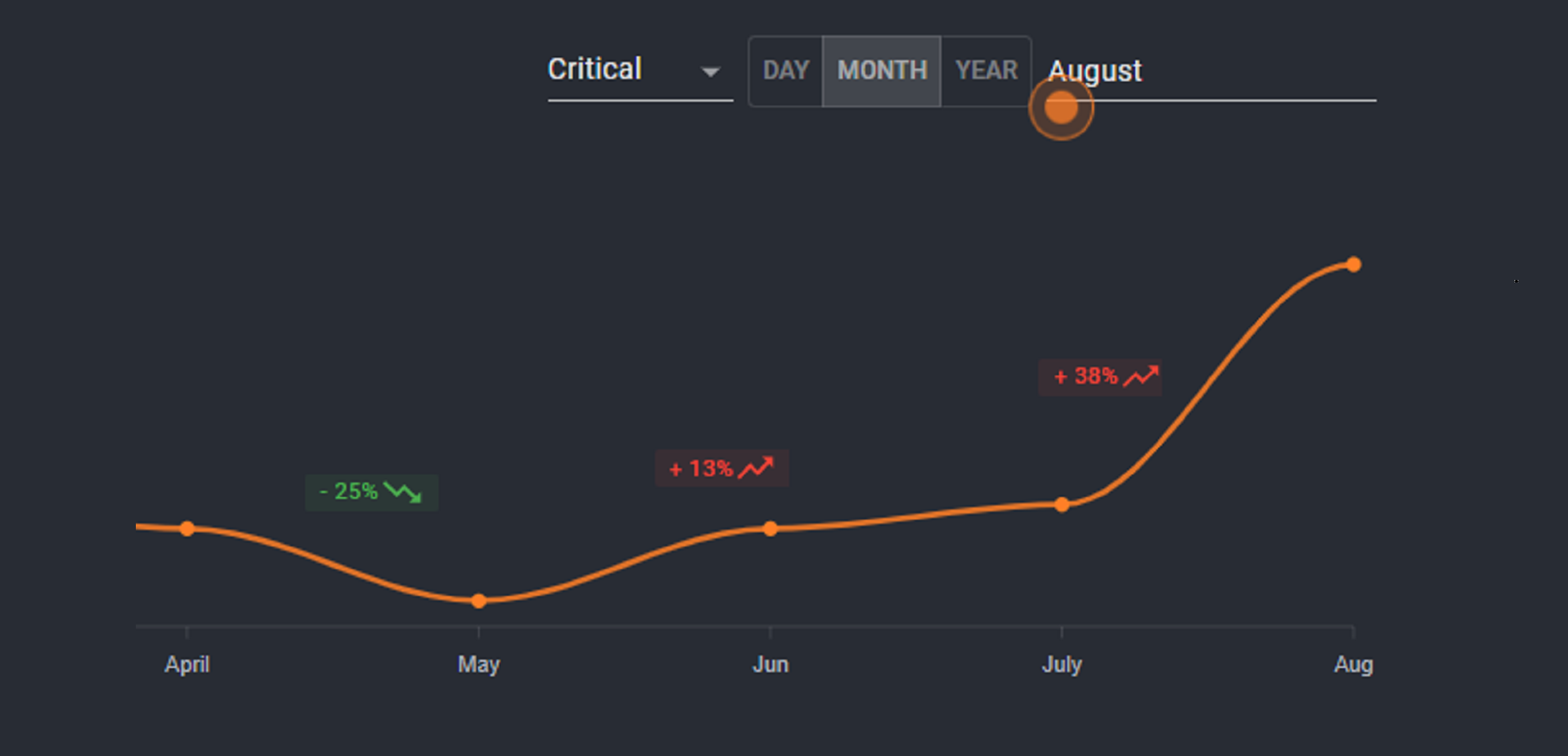
MONITOR
Determine for the requested time period, whether your implemented security measures are working or becoming critical.
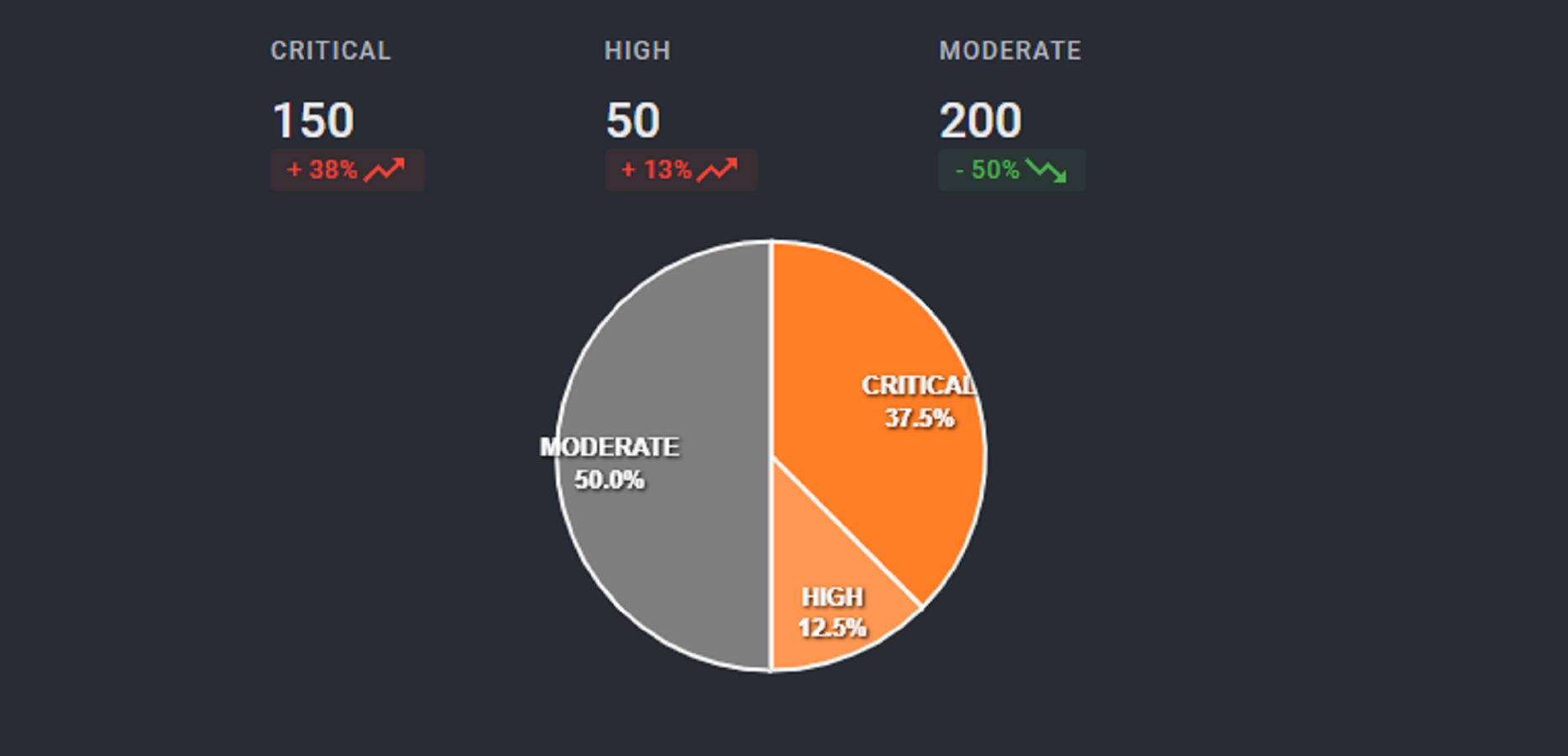
RATING
Identify which issues are critical, high, moderate and how they are spread in the enterprise across users and devices.