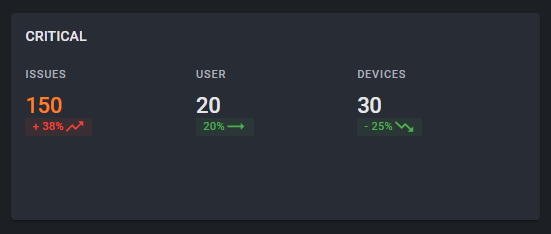
Distribution of risks
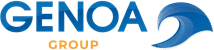
Identify the level of critical IT risks through
- Number of mobile devices / users affected
- Change (+/-)
For the comparison period, the price indicator shows whether the risk is reduced or not.
How many issues are critical?
Determine how severe the impact of security vulnerabilities is.
- Critical
- High
- Moderate
Prioritize the measures for critical mobile devices and make decisions based on relevance.
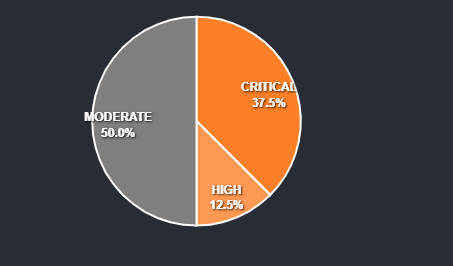
Live data shows how security measures are working
Determine how risk mitigation measures are performing for the desired time period and make appropriate follow-up decisions based on current data.
Time period
Choose the period of observation according to your needs.

DASHBOARD
Keep an eye on all critical security vulnerabilites and see on 1-click on which device they are located.
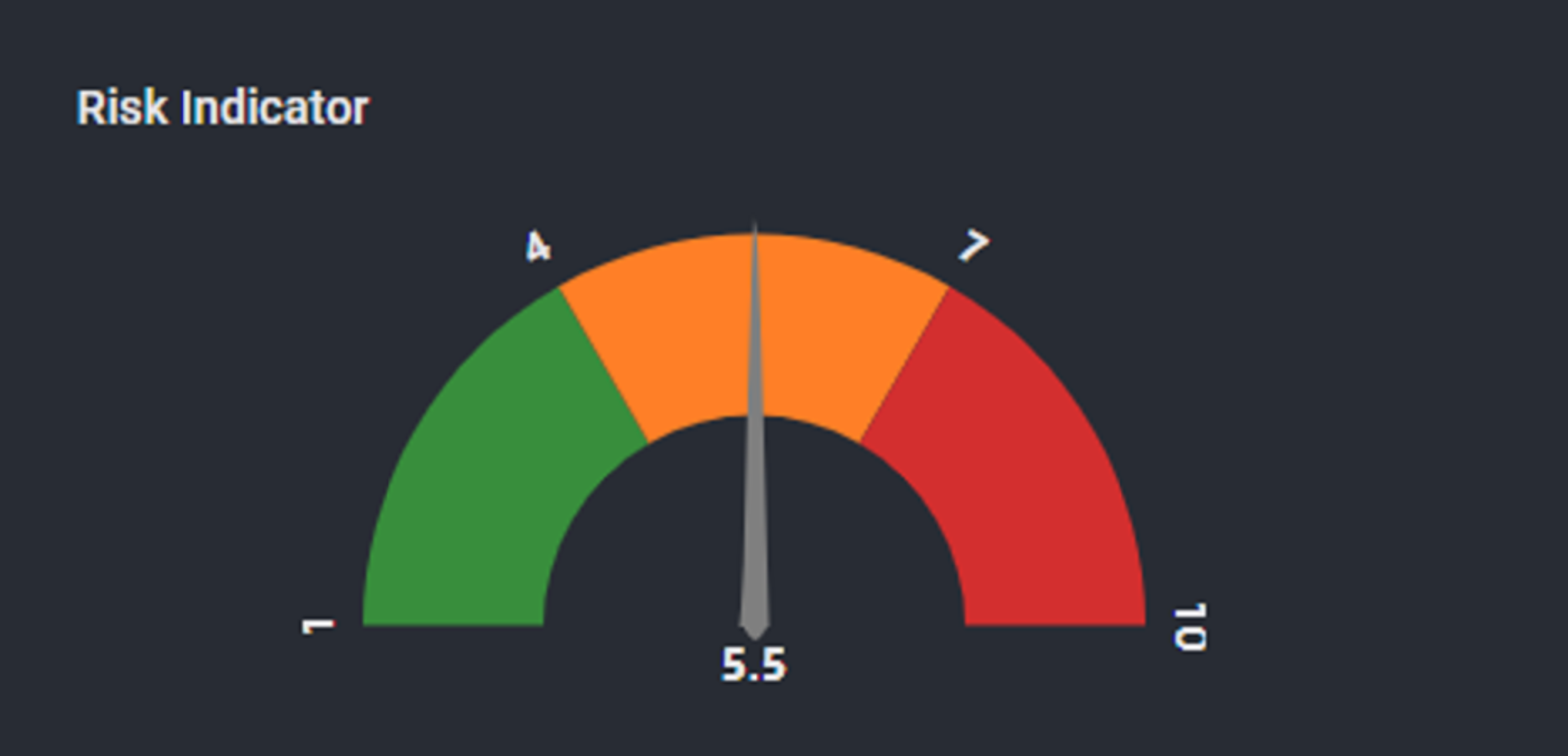
KPI
Use the Risk Indicator to determine the current security status of your company or your sub-organizations.
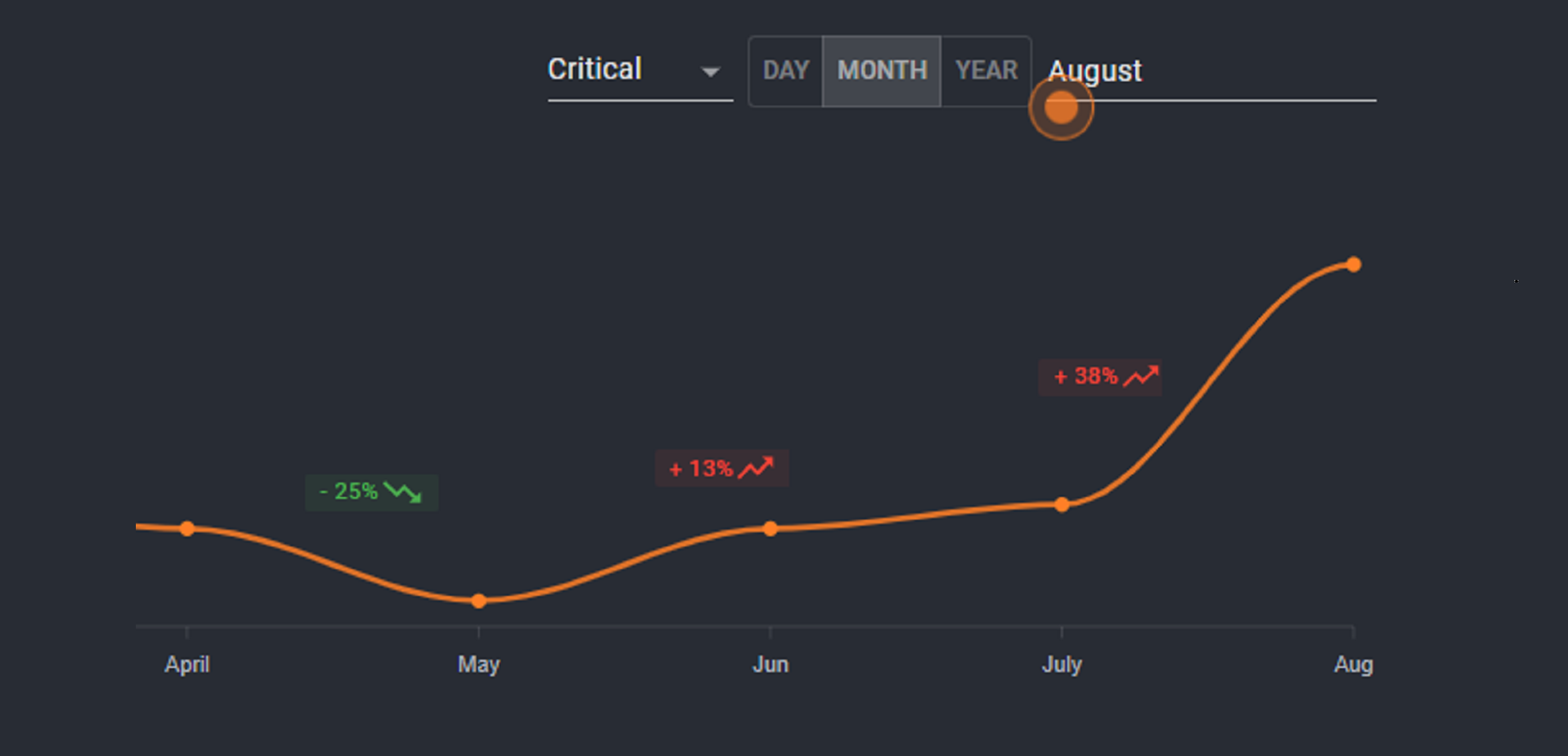
MONITOR
Determine for the requested time period, whether your implemented security measures are working or becoming critical.
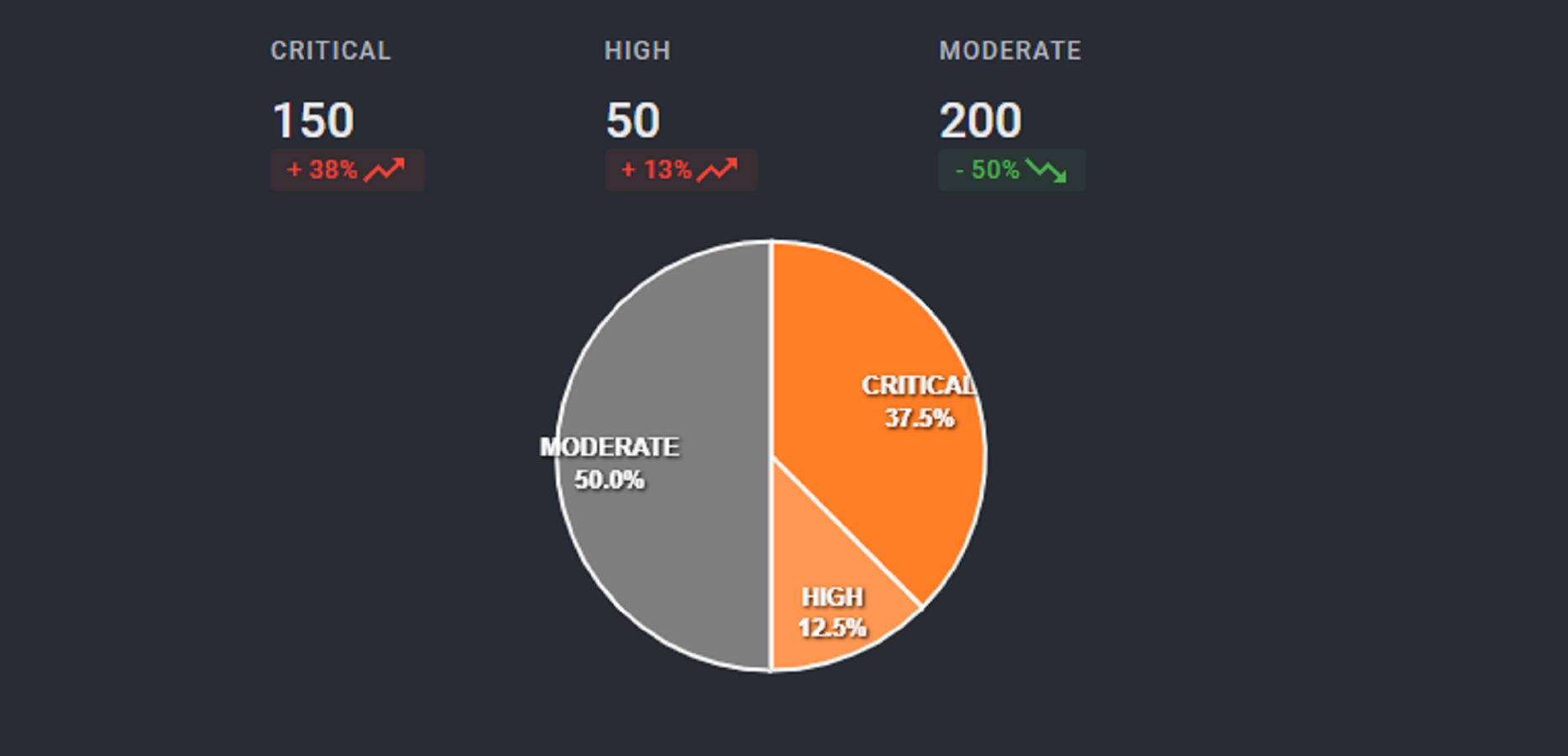
RATING
Identify which issues are critical, high, moderate and how they are spread in the enterprise across users and devices.